Author: Thierry Julien, CEO of TJC Group
Decommissioning legacy systems is one of the crucial factors that organisations must consider. Not only does it help against future compliance requirements, but also against cyberattacks and data privacy breaches. Here’s a take on why decommissioning is the safest bet today.
Millions of personal data revealed because of a data breach!
A couple of months back, I came across a striking headline on 01net magazine that read, “The DNA of 2.1 million people has been hacked due to an unimaginable negligence”.
The story begins classically: a company is extorted and asked to pay for a ransom. A software called Cobalt Strike was able to penetrate the network of DNA Diagnostics Centre (DDC), an American healthcare organisation specialising in DNA and paternity testing.
The software got hold of the organisation’s databases, accessing millions of personal data. When this intrusion was detected, the alerts were incomprehensibly ignored. For an unknown reason, DNA Diagnostics Centre did not immediately react to the warning from its security provider.
However, what’s more interesting, is that the software turned out to be the same one that Cybersecurity experts use to test system resistance.
All in all, the results of the intrusion were heavy, damaging the company’s reputation, along with the imposing critical fines. Not to mention, the serious knock-on effect for the victims, such as the disclosure of health and personal data.
While it is all too common in our newspapers, what makes this case special is we are talking about the involvement of servers and databases, instead of one single application. As reported by the US Federal authorities: “Five servers were compromised and contained backups of 28 databases, and a decommissioned server was used to exfiltrate data”.
A legacy system, the epicentre
These servers were likely virtual machines, particularly vulnerable when left unattended. But what makes this article interesting is the reason for such negligence – the stolen data was legacy data relayed when DDC acquired a smaller company in 2012. The DNA testing specialist admitted not having the faintest idea that such data was stored on its servers.
As reported in the article: “DNA Diagnostics Centre specialist ensures that a previous inventory of its archives had not revealed the presence of the data”.
As it stands, leaving a server on “stand-by” ended up being a crushing negligence. It is such carelessness with the management of legacy systems that put DDC into serious trouble. Legacy systems are no longer updated and receive no support or maintenance. Therefore, they are also overexposed to security vulnerabilities, which is why one must decommission legacy servers to protect that data.
Now, claiming ‘carelessness’ is far too easy. The real question is – how often did we ‘backup’ information and servers over the years? The move to the cloud and the data privacy regulations have made such old practices that used to be safe a significant risk that is no longer acceptable. Hence, a Legacy System Application is becoming the norm today!
The flip side of Virtual Machines
Virtual Machines (VM) are seen as a feasible and quick solution to store legacy systems. However, VMs pose three serious pitfalls when used as a decommissioning solution:
- VMs do not provide the option to manage Data Privacy obligations, exposing the company to compliance risks.
- They allow organisations to ‘dump and forget’ information. The day the employees leave the project, or the company, or go on retirement, it will be difficult to identify the potentially harmful information.
- VMs are more vulnerable to custom ransomware designed to cripple these technologies.
That is why, in the situation presented in this article, the safest bet for DNA Diagnostics Centre would have been, without hesitance, to decommission the acquired legacy system.
You can find out more on Virtual Machines here: Virtual Machines to maintain legacy systems: a good or bad idea?
System decommissioning, a safe bet
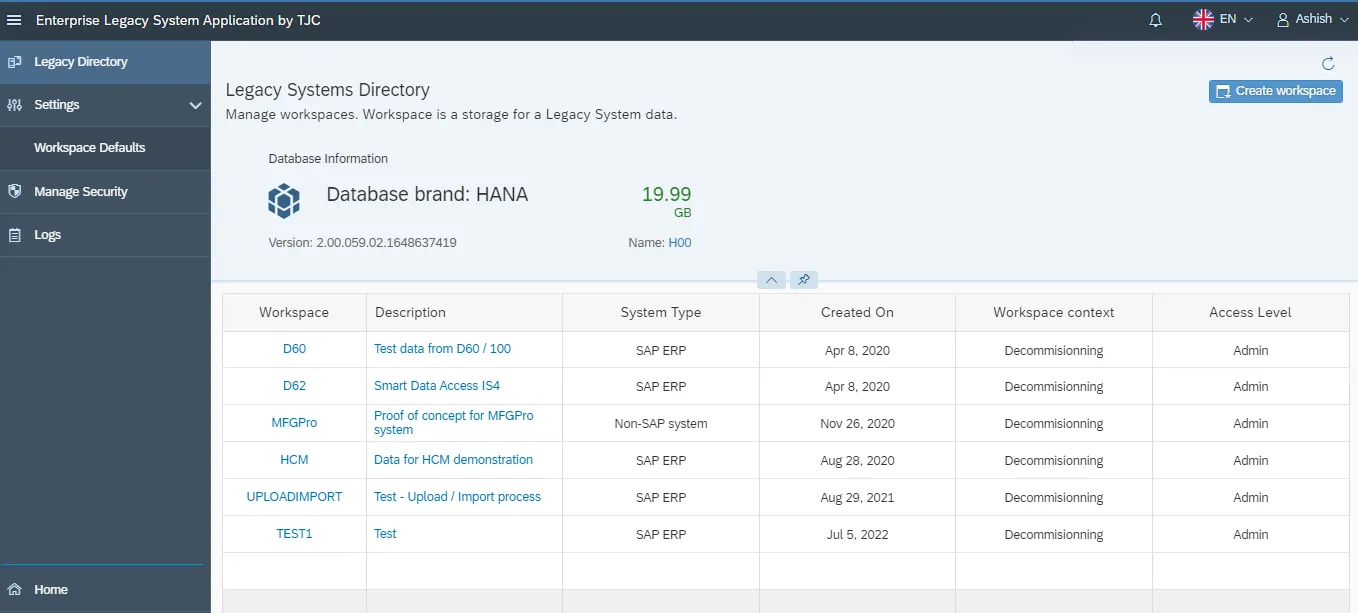
The decommissioning of legacy systems allows enterprises to retain access to the legacy data (most of the time, for business needs or audits) whilst applying necessary data privacy controls when required. If the legacy system that DDC acquired was relevant or data sensitive, it should have been managed by a Legacy System Application, such as ELSA by TJC Group. Enterprise Legacy System Application is SAP BTP-certified solution that ensures all legacy data can be re-accessed at any time, from any source, after retiring an old system.
Final takeaways
There are several reasons a company might want to decommission a legacy system – one of which is to protect the organisation against cyberattacks or future compliance requirements, both being factors outside of our control.

If legacy systems are not decommissioned, there is a high risk of future exposure to “bombshells”. On the other hand, legacy systems are based on old technologies that will, sooner or later, become outdated. Finding IT professionals that have that niche talent can be challenging and costly to hire, while the new employees will not have the knowledge to deal with future issues.
As a final word, it is imperative to note that all IT systems containing sensitive information should be decommissioned – and not just “sunset”. If you need further information or assistance to retire a legacy system, get in touch with us.
Sources of information
- L’ADN de 2,1 millions de personnes a été piraté à cause d’une incroyable negligence, 01net magazine.
- Re-thinking the security of virtual machines, CSO Online
- Are virtual machines the new gold for cyber criminals?, Mcafee.









